8 Terrifying Security Flaws in Your Wi-Fi—And How to Fix Them
Your network may have holes that could bring hackers and federal agents to your front door.
Sep 6, 2023 | Share
FAQ, Technology
All wireless devices encrypt their connections by default. Well, usually. Some public Wi-Fi networks may not use encryption even if your device does, which is why you should use the best VPN tools in that case or tether from a mobile internet connection instead.
But at home or in the office? We connect our devices to Wi-Fi and think nothing more of it. It’s super secure, right? Right??
Maybe. Maybe not.
Your connections are encrypted, sure, but is your gateway or router fully secure? Are all the security holes patched to keep hackers out? Did you create an uncrackable password? If you can’t say “yes” to any of these questions, then your network is in dire need of a security check. Like, pronto. We walk you through a list of security flaws and tell you how to fix them.
Do you have the most secure internet you can get?
All internet providers generally stay on top of security, but if you think your current provider fails to keep you safe, enter your zip code to see what else is available to you.
Flaw #1: Outdated firmware leaves you vulnerable
Firmware is another name for the router’s operating system. It’s software that manages the hardware, and like any other operating system, it’s never fully bulletproof—there are always gaps in the code that can give unwanted hackers access to your network.
The good news is software engineers continuously fill these holes with new updates. The bad news is your router may not automatically update the firmware to the latest, most secure version, leaving your network wide open for a possible remote attack.
Solution
Nearly all standalone routers, gateways, and mesh systems enable automatic firmware updates by default. You’re normally required to enable this feature during the setup, or it’s already enabled, and the router checks for new updates before you can use it.
But there are exceptions. We’ve tested a few ASUS routers that don’t have auto updates enabled out of the box. Yes, the possibility of a failed update is real and could leave your router as an expensive paperweight, but the chances of that happening are extremely rare.
That said, we provide a separate guide on how to update your router’s firmware to the latest and greatest version.
Flaw #2: Easy Wi-Fi passwords invite strangers and hackers
Creating an easily guessed Wi-Fi password based on something familiar—like a child’s name, a pet, or your address—is convenient for sure, but it also leaves your Wi-Fi network vulnerable to hackers lurking nearby.
Solution
Unlike the admin password, most modern routers, gateways, and mesh systems don’t force you to create a unique Wi-Fi password. The supplied one is already unique to that device—which wasn’t the case in years past—but you should change it to be safe. The complexity of it depends on you, but remember, you can always share the Wi-Fi login credentials using a QR code or another method supported by the router’s mobile app. We provide a separate guide on how to share your Wi-Fi password from your phone.
Still, we suggest using a passphrase with letters (upper and lower), numbers, and symbols. For example, “Ch!ck3nP33k@b00” uses unrelated words and is much harder to guess and crack than “h0m3n3tw0rk.” You can also use a password manager to create your password or allow your mobile devices to make one for you, which is usually just a string of numbers and letters you’ll never remember but is easy to retrieve from your device’s settings.
Check out our guide on how to change your Wi-Fi password for more information.
Flaw #3: Using the router’s default login can leave you open to hackers
Your router has a public side (the internet) and a private side (your home network). That means anyone can access your router—whether it’s remotely or locally—if you have the worst router login credentials ever created. An easily cracked password allows hackers to infiltrate your router, gateway, or mesh system and control your entire network—including your wired and devices.
Solution
This issue really only applies to older routers that accept commonly used login information like admin/password. Modern routers, gateways, and mesh systems now force you to create a unique administration password during the setup using letters (upper and lower), numbers, and symbols—there’s no getting around it.
But if you have an older router or gateway and you never changed the login username and password, do so now. Consult our guide on how to log in to your router using a web browser (or an app if your router supports it)—the setting you want is usually found under Advanced > Administration. Most mesh systems don’t have a web interface you can use, so you can change the info only in the app.
Flaw #4: WPS opens your network to hackers
Wi-Fi Protected Setup (WPS) helps devices connect to your wireless network upon first use without the need for a password. You either press a button on the router or use an eight-digit PIN.
But there’s a consequence for that ease of use: WPS is vulnerable to brute-force attacks, which is a trial-and-error method to determine login info.1 A hacker could discover the PIN’s first four digits—there are only 11,00 possible combinations—and then uncover the next four. Free tools you can easily download from the internet can crack the PIN in 4 to 10 hours.
Solution
Your best defense is to update your firmware and disable WPS (if possible). The method of disabling WPS depends on the manufacturer, but here we’ll use the NETGEAR Nighthawk RAX80 as an example.
Using the web interface
Step 1: Connect to the router’s Wi-Fi.
Step 2: Open a browser and type in routerlogin.net.
Step 3: Click on the ADVANCED tab displayed on the left.
Step 4: Click on WPS Wizard listed on the left and follow the instructions to disable this feature.
Flaw #5: Guests can download illegal content
There’s nothing wrong with giving friends and external family members access to your home’s network, but you also don’t want them downloading questionable content using your internet connection. You certainly don’t want the FBI knocking at your door, and that could happen if guests download anything they want.
Solution
Create a second “guest” connection for everyone who lives outside your home. This virtual network keeps visitors off your primary connections and limits the number of devices that have access. Plus, you’re not sharing your main network’s password.
With a guest network, you can limit bandwidth, block websites, set connection times, and more per device. We provide a separate guide on how to set up a guest Wi-Fi network.
Flaw #6: Children have unlimited access to explicit content
The internet is both a blessing and a curse for parents. On one hand, kids and teens can find the information they need. They can play games online with friends and take remote classes. Unfortunately, they can access inappropriate and unwanted content with just a single URL.
Solution
We provide a guide on how to set up parental controls on a router to protect your kids and teens. Here, you can block and allow specific sites, block and allow specific devices, and set hours of use.
Some routers handle parental controls through a specific section within the router’s interface. You can also click on a device to manage the connection, use profiles to set the parental controls for each child, and manually block websites you don’t want the entire house or office to access.
Parental controls aren’t just for children
You can use parental controls to restrict devices used by adults so you can limit the content they can access, the websites they can visit, and when they can connect.
Flaw #7: Remote access invites hackers
Remote access allows you to load the router’s interface over the internet, like from a hotel room in another state. Combined with a default or lousy password, anyone can gain access from anywhere and change its settings to route all your internet traffic to nefarious websites.
Solution
Old-school remote access through the web interface really isn’t a thing anymore. Many routers still include it, but it’s disabled by default since it’s such a security risk. You can typically find Remote Access controls in the router’s Administration section if you ever need to use it or simply want to verify it’s toggled off.
However, modern routers, gateways, and mesh systems now allow you to manage your network from afar through a mobile app and a linked cloud account, so you really don’t need the web-based remote management tool anymore.
Flaw #8: Your router broadcasts the manufacturer’s name
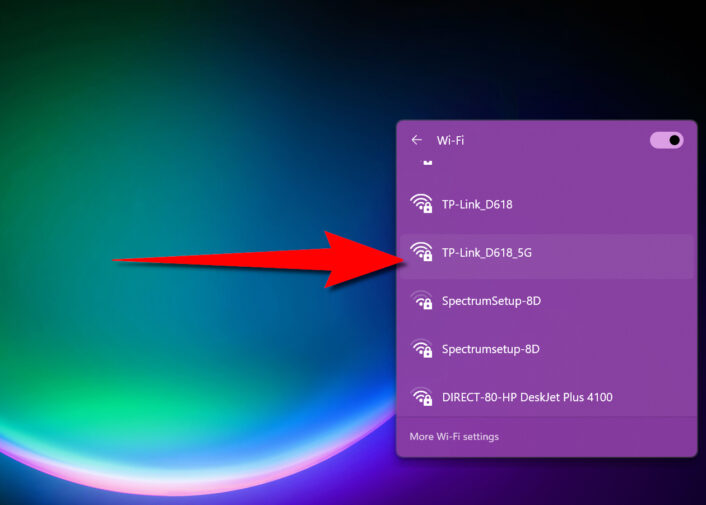
Click or tap on your device’s Wi-Fi icon, and chances are you’ll recognize some of the names on the resulting list: Linksys, NETGEAR, and so on. Owners of these routers never changed the default Service Set Identifier (SSID) name, which is the wireless network’s public name.
Why is that a problem? Anyone who sees “Linksys” or “NETGEAR” will know that someone owns one of these routers. With this information, hackers can launch an attack tailored to your router, break into your network, and steal your data.
Solution
Generally, you’re encouraged to change the default SSID during the setup. If you disable Smart Connect (band steering), you create a new SSID for each band. You can rename them to anything, whether it’s something simple or a label just to annoy your neighbors. Have fun or be practical—it’s all up to you.
If you never changed the SSID, you can do so through the mobile app provided by the manufacturer or by using the web interface. The following instructions use the TP-Link Archer AXE75 router as an example.
Using the web interface
Step 1: Connect to the router’s Wi-Fi.
Step 2: Open a browser and type in tplinkwifi.net.
Step 3: Select Wireless listed on the left.
Step 4: Select the Wi-Fi connection you want to change.
Step 5: Enter the new SSID name and save your changes.
Using the Tether app
Step 1: Connect to the router’s Wi-Fi.
Step 2: With the Home tab selected, tap on Wireless.
Step 3: Select the Wi-Fi connection you want to change.
Step 4: Enter the new SSID name and save your changes.
Author - Kevin Parrish
Kevin Parrish has more than a decade of experience working as a writer, editor, and product tester. He began writing about computer hardware and soon branched out to other devices and services such as networking equipment, phones and tablets, game consoles, and other internet-connected devices. His work has appeared in Tom’s Hardware, Tom's Guide, Maximum PC, Digital Trends, Android Authority, How-To Geek, Lifewire, and others. At HighSpeedInternet.com, he focuses on network equipment testing and review.
Editor - Cara Haynes
Cara Haynes has been editing and writing in the digital space for seven years, and she's edited all things internet for HighSpeedInternet.com for five years. She graduated with a BA in English and a minor in editing from Brigham Young University. When she's not editing, she makes tech accessible through her freelance writing for brands like Pluralsight. She believes no one should feel lost in internet land and that a good internet connection significantly extends your life span.




